5 Critical Cybersecurity Best Practices for Modern Microgrids
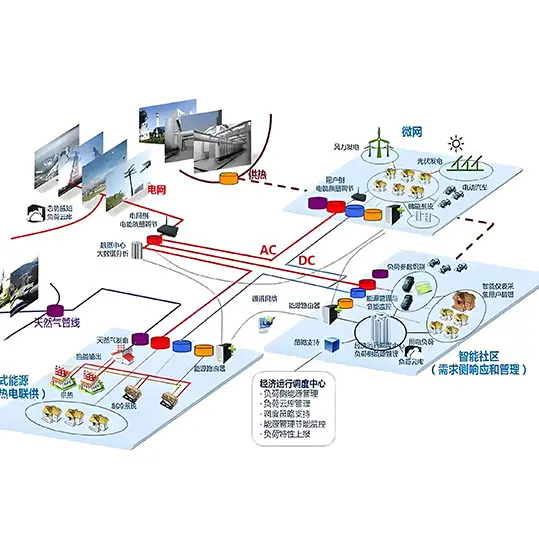
As microgrid deployments accelerate globally to support energy resilience and renewable integration, cybersecurity has emerged as one of the most critical concerns for system owners and operators. Unlike traditional centralized power grids, microgrids often operate in distributed locations with multiple connected devices – from inverters and BESS controllers to monitoring systems – creating more potential attack surfaces.
In recent years, we’ve seen a growing number of cybersecurity incidents targeting energy infrastructure, and microgrids are no exception. A successful cyberattack can compromise system operations, cause financial losses, and even threaten public safety. Therefore, implementing robust cybersecurity measures is not just an option – it’s a necessity for any modern microgrid project.
Understanding the Cybersecurity Landscape for Microgrids
Microgrids face unique cybersecurity challenges compared to traditional centralized power systems. Because they typically incorporate more IoT devices, communicate over public networks for remote monitoring and control, and often operate in isolation or semi-isolation from the main grid, they require specialized security approaches that differ from conventional utility practices.
Many microgrid projects are located in remote or unattended sites, from mining operations and industrial facilities to rural community power systems. This physical remoteness can make them more vulnerable to both physical attacks and cyber intrusions, as on-site security personnel may be limited or non-existent. Additionally, because microgrids often integrate multiple third-party components from different manufacturers, ensuring consistent security across all devices can be challenging.
Common threats include unauthorized access to control systems, malware attacks on communication networks, ransomware that can lock critical operations, distributed denial-of-service (DDoS) attacks that overwhelm system resources, and physical tampering with remote sites. According to recent industry reports from the U.S. Department of Energy, nearly 60% of microgrid operators have experienced at least one cybersecurity incident in the past five years, with an average recovery cost exceeding $200,000 per incident. This data clearly highlights the urgency of addressing cybersecurity issues in microgrid projects.
The evolving nature of cyber threats means that security measures must also evolve continuously. Attackers are constantly developing new techniques and discovering new vulnerabilities, so what was considered secure five years ago may not be adequate today. The good news is that with proper planning and implementation, most cybersecurity risks can be effectively mitigated. Let’s explore the five critical best practices that every microgrid operator should implement to protect their system.
1. Implement Network Segmentation
Network segmentation is the practice of dividing your microgrid’s network into smaller subnetworks, so that if one segment is compromised, the attack cannot easily spread to other parts of the system. For example, you can separate the operational technology (OT) network that controls power electronics from the information technology (IT) network used for business communications.
In a typical microgrid, this means placing firewalls between the control network for PCS, MPPT, and battery management systems and the external internet. Only necessary communication should be allowed through designated gateways, and all other traffic should be blocked.
This approach dramatically limits the potential damage from a cyber breach. Even if an attacker gains access to one part of the system, they cannot easily reach the critical control components that keep the microgrid running. Many security experts consider network segmentation to be the single most effective cybersecurity measure for microgrids.
2. Regularly Update and Patch All Devices
One of the most common ways attackers gain access to microgrid systems is through unpatched vulnerabilities in software and firmware. Many microgrid components – including inverters, controllers, and monitoring equipment – may remain in service for 10-20 years, and operators often forget to update them with the latest security patches.
Establishing a regular patch management program is essential. This should include:
- Maintaining an inventory of all connected devices and their software/firmware versions
- Monitoring security advisories from component manufacturers
- Testing patches on a non-production system before deploying them
- Applying critical security patches within a reasonable timeframe
For legacy devices that no longer receive security updates from manufacturers, consider compensating controls such as additional network filtering or moving them behind stricter firewall rules. Even when end-of-life is reached, you can still protect these devices through network segmentation and monitoring.
3. Enforce Strong Access Control
Access control is another fundamental aspect of microgrid cybersecurity. Every user and every device should have only the minimum level of access necessary to perform their functions – this is known as the principle of least privilege.
Key access control measures include:
- Requiring multi-factor authentication (MFA) for all remote access to control systems
- Using strong, unique passwords for all accounts and changing them regularly
- Immediately revoking access when employees or contractors leave the project
- Implementing role-based access control (RBAC) to limit what each user can do
- Using secure key management for device-to-device authentication
It’s also important to regularly audit access logs and look for suspicious activity. Many attacks are discovered through anomalous login patterns, so continuous monitoring can help detect breaches early before they can cause significant damage.
4. Encrypt Sensitive Communications
Microgrids rely on communication between multiple components – from sensors scattered across the site to central controllers and remote monitoring platforms. All of this communication should be encrypted to prevent eavesdropping and tampering.
For communications traveling over public networks, such as when a microgrid operator monitors the system from a remote location using a mobile app, encryption is absolutely essential. Use modern encryption protocols like TLS 1.3 for all web-based communications, and encrypted VPNs for remote access to control networks.
Even for communications within the local microgrid network, encryption adds an important layer of protection. If an attacker does gain access to one segment of the network, encrypted communications are much more difficult to intercept and manipulate. This is particularly important for control signals that affect DCDC conversion, power routing, and battery charging/discharging.
5. Conduct Regular Security Audits and Testing
Cybersecurity is not a one-time project – it requires continuous monitoring and improvement. Regular security audits and penetration testing can help identify vulnerabilities before attackers do.
At a minimum, you should conduct a comprehensive security audit at least once a year, and after any major changes to the microgrid system. This should include:
- Vulnerability scanning to identify known security issues
- Penetration testing by qualified cybersecurity professionals to simulate real attacks
- Reviewing access controls and security policies
- Testing incident response plans to ensure they work effectively
Many insurance companies now require regular security audits before they will provide coverage for cyber risks, so this can also help with risk management and insurance costs. A professional security audit will typically provide you with a prioritized list of recommendations for improving your security posture.
Integration with Microgrid solution Design
It’s important to remember that cybersecurity should be considered from the very beginning of the microgrid design process, not added as an afterthought. Many project owners make the mistake of focusing exclusively on power performance, cost, and reliability during the design phase, only addressing cybersecurity at the end – if at all. This approach often leads to expensive retrofits and suboptimal security outcomes.
When working with an experienced provider like Imaxpower, cybersecurity is built into the system architecture from day one. We consider security implications at every stage of the design process, from component selection to network architecture to ongoing maintenance. Our approach ensures that security doesn’t impede system functionality while still providing robust protection against threats.
Our power-router systems incorporate multiple layers of security, including hardware-enforced security boundaries, regular firmware updates delivered through secure channels, and end-to-end encrypted communications between all system components. This defense-in-depth approach ensures that your microgrid remains protected against evolving cybersecurity threats throughout its lifecycle. We also provide ongoing security guidance and can help you implement a sustainable security management program for your operation.
A well-designed microgrid with proper cybersecurity measures in place doesn’t have to be significantly more expensive than an unsecured system. The additional investment in security typically represents just 2-5% of the total project cost, but it can save you from potentially catastrophic losses in the event of an attack. When you consider the potential cost of downtime, recovery, and reputational damage, the return on investment for strong cybersecurity is clear.
Conclusion
As microgrids become more connected and widespread, cybersecurity will only grow in importance. By following these five critical best practices – network segmentation, regular patching, strong access control, encryption, and regular testing – you can dramatically improve your microgrid’s security posture and reduce the risk of successful cyberattacks.
Remember, no system can ever be 100% secure, but implementing these practices will make your microgrid a much harder target for attackers, and ensure that if an incident does occur, you can respond quickly and minimize the damage. A secure microgrid is a reliable microgrid, and reliability is what microgrids are all about.
Contact Imaxpower for Your Microgrid Project
Looking to design and deploy a secure, resilient microgrid for your site? Contact Coco at Imaxpower today for expert guidance and customized solutions.
Contact: Coco
Phone: +86-13760212825
Email: info@imaxpwr.com
We specialize in designing and building high-performance microgrids with the latest cybersecurity protections built-in. Send us your inquiry today to discuss your project requirements and get a customized quotation.